Redesigning DeFi Cybersecurity.
- id-bound
- Apr 16
- 6 min read
Updated: 24 hours ago
In the rapidly converging worlds of Decentralized Finance (DeFi) and Real-World Assets (RWAs), capital efficiency has long been the "holy grail." Traditional RWA tokenization often forces a binary choice: keep your assets safe in a locked vault or put them to work in a high-risk DeFi pool. rTRIO shatters this trade-off by introducing a Conditional Bearer Asset Architecture that balances absolute security with instant, global liquidity.
rTRIO as a redeemable loan.
At the heart of the system is a 1:1 USDC-guaranteed proxy token called rTRIO. Unlike traditional collateral models—where depositing an asset into a protocol often creates a "blind" seizure risk—the rTRIO model uses Identity-Linked Vaulting.
The Protected Layer: When a user locks TRIO tokens in a secure, self-custodial Collateral Account, they mint rTRIO as a redeemable loan. Crucially, the original TRIO stays in a locked account under the user's name, shielded from external protocol smart contracts.
The Liquid Layer: The rTRIO serves as a "Smart Letter of Credit" that can be traded, used as collateral, or held in escrow.
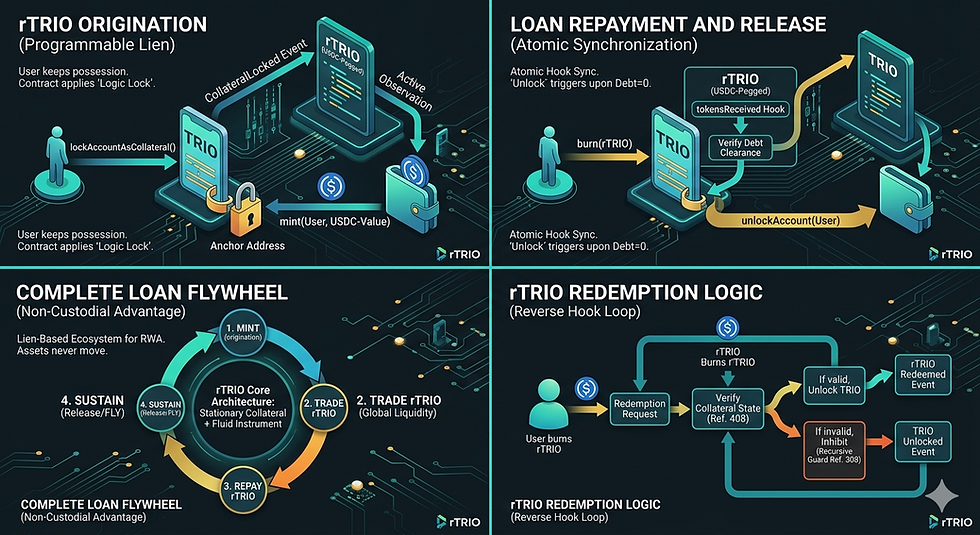
The following infographics illustrate the end-to-end lifecycle of a TRIO-collateralized loan using the advanced capabilities of the rTRIO protocol.
Infographic 1: rTRIO Origination (Programmable Lien) This diagram visualizes how the user originates a loan.
The User initializes the lockAccountAsCollateral() event, which triggers the TRIO smart contract. A "Programmable Lien" clamps onto the stylized TRIO wallet (the Anchor Address).
Crucially, the user keeps possession. Only the Logic Lock moves to the smart contract.
A CollateralLocked event is emitted. The rTRIO (USDC-Pegged) contract performs Active Observation, and once the Mempool Scanner confirms the lock is stable, it mints the USDC-Value tokens into the user's wallet.
Infographic 2: Loan Repayment and Release (Atomic Synchronization). This diagram visualizes how the loan is repaid.
The User initiates the burn(rTRIO) command, sending the USDC-pegged debt obligation back to the contract.
The internal logic of the rTRIO contract triggers the tokensReceived Hook and simultaneously runs the Verify Debt Clearance routine.
Upon successful verification, the rTRIO contract executes the unlockAccount(User) command. This creates a Reverse Hook Loop that removes the Logic Lock from the user's wallet address.
Infographic 3: Complete Loan Flywheel (Non-Custodial Advantage) This flowchart summarizes the "Lien-Based Ecosystem" for RWAs.
Unlike traditional models, the assets (TRIO and rTRIO) are always in the possession of the user.
The flywheel shows the circular lifecycle:
1. MINT (Origination),
2. TRADE rTRIO (Global Liquidity),
3. REPAY rTRIO (Repayment Loop), and
4. SUSTAIN (Release/FLY).
This cycle ensures that the RWA issuer benefits from global liquidity without assuming the risk of a centralized exchange or bridge failure.
Infographic 4: rTRIO Redemption Logic (Reverse Hook Loop) This diagram provides a deep dive into the security of the redemption logic.
When a user burns rTRIO to redeem the underlying asset value, the system creates an atomic state flow: User burns rTRIO -> Verify Collateral State -> Check Mempool Status.
A fork in the logic:
If valid: The system unlocks TRIO and emits the relevant events.
If invalid (e.g., pending liquidation or de-peg): The Recursive Guard Inhibits the unlock, preventing a "Race Condition" exploit.
Solving the DeFi "Trap": The Circuit Breaker
In standard ERC-20 interactions, a transferFrom approval is an unconditional "blank check." The rTRIO architecture replaces this with Programmatic Enforcement, acting as a circuit breaker for liquidations.
Proxy-Only Seizure: A DeFi protocol never touches the underlying TRIO. It only has the authority to seize the rTRIO proxy.
Oracle Gatekeeping: Before any seizure can occur, the rTRIO smart contract executes a mandatory check via the rTRIOOracle.
Automatic Reversion: If the oracle does not validate that the user is in default (Health Factor < 1), any attempt to seize the rTRIO is automatically reverted.
Stable Exit: Upon a valid default, the protocol seizes the rTRIO and swaps it for USDC via an internal smart contract. The lender is repaid in stable value, and the underlying TRIO is only forfeited after an rTRIO loan default.
Versatile Applications
The versatility of the rTRIO bearer asset extends into multi-billion-dollar institutional markets:
Real-World-Asset: RWA tokenisation.
Trade Finance: Using rTRIO as a digital Letter of Credit, where payment is programmatically released only upon verified delivery of goods.
Tokenized Deposits: Using rTRIO (pegged to USDC) to purchase interest-bearing, bank-issued tokenized deposits, allowing retail investors to access institutional-grade yield without leaving the ecosystem.
E-Commerce: using rTRIO (pegged to USDC) within TRIO E-Commerce Hosted Gateway.
Institutional DeFi enablement:
If a market fluctuates, you have time to pick up the phone, call your banker, and rectify a collateral shortfall. However, as we move toward the 2026 Digital Asset Standard, the transition to automated DeFi protocols has introduced a lethal new risk: the Algorithmic Liquidation Cascade.
For a trade finance house managing millions in tokenized commodities, a 30% flash crash in the underlying collateral (like ETH) shouldn't result in an instantaneous, bot-driven seizure of assets. Yet, in legacy DeFi, that is exactly what happens. rTRIO changes this by introducing the "Dual-Gated Recursive Guard."
The Problem: The Censorship of the "Right to Cure"
In a standard liquidity crisis, two things happen simultaneously: asset prices plummet and network congestion skyrockets. When a trader’s health factor drops, they attempt to "top up" their collateral. However, because thousands of others are doing the same, gas fees spike. Their transaction gets stuck in the mempool. In the eyes of a traditional smart contract, that transaction doesn't exist until it’s mined. The contract sees a breach, executes an immediate seizure, and the trader loses their collateral—even though they tried to pay.
The rTRIO Solution: USDC Anchoring & Recursive Verification
rTRIO solves this through three specific technical innovations designed for institutional trade:
Asset Anchoring: Unlike "wrapped" assets that move across risky bridges, rTRIO uses a Stationary Ethereum Model. Assets are pegged to USDC. This ensures the collateral continues to provide the same "Finality" found in traditional banking.
The Dual-Gated "AND-Gate": Seizure cannot happen through price alone (Gate A). It requires a second, fiduciary attestation (Gate B) confirming that a 24-hour Grace Period has expired. This synchronizes the speed of the blockchain with the reality of commercial law.
The Recursive Mempool Scanner: This is the "Safety Valve." Immediately before a seizure is executed, the rTRIO system performs a Recursive State Check. It scans the network’s pending transaction pool. If it sees the trader's "Top-Up" transaction sitting in the mempool, it inhibits the seizure. It recognizes the "intent to cure," preventing the network’s own congestion from being used as a tool for asset theft.
Conclusion
The rTRIO architecture represents a fundamental shift from probabilistic security (relying on market bots and protocol integrity) to deterministic safety (relying on mathematical proof and internal logic). By providing developers with a production-ready environment for testing, TRIO is set to become the "Gold Standard" for RWA collateral, bridging the gap between institutional safety and DeFi innovation.
More advantages of rTRIO.
The "Jurisdictional" Angle: Stop "Wrapping" your assets. Start "Anchoring" them. ⚓⚖️
In the rush to go "Cross-Chain," we’ve created a "Bridge Crisis." Every time you bridge an asset, you lose its legal origin and increase your risk of smart contract exploits.
rTRIO introduces the Stationary Ethereum Model. With rTRIO, your primary asset (the USDC) is never in jeopardy.
Global Utility: Trade the bearer tokens anywhere, in KYC compliance.
Local Security: This is how we bring the Rule of Law to the Speed of Code. No bridges. No wrapped-asset risk.
In the 2026 digital asset landscape, the "problem" is technically known as The Bridge Vulnerability Gap and The Legal Fragmentation of Title:
1. The "Honey Pot" Risk (Technical Reference):
The primary technical reference is the 2022-2024 Cross-Chain Bridge Exploits (e.g., Ronin, Wormhole, Nomad).
The Problem: Moving an asset across a bridge requires "locking" it in a smart contract on Chain A and "minting" a representative token on Chain B. This creates a massive, centralized "Honey Pot" of idle assets.
The rTRIO Advantage: By using USDC Anchoring, the asset never enters a bridge contract. You aren't moving the "Gold"; you are moving the "Warehouse Receipt" (the Bearer Token).
2. The "Lex Cryptographia" Conflict (Legal Reference):
Refer to the UNIDROIT Principle of Digital Assets (2023/2024 updates).
The Problem: When you move a digital asset across chains or into "wrapped" versions, you often trigger a "No-Man 's-Land" Jurisdiction. If a wrapped token is stolen, which country's law applies? The chain of custody is often legally severed.
The rTRIO Advantage: Swap to USDC anywhere.
3. The "Insolvency of the Wrapper" (Financial Reference):
Reference the 2024 "Wrapped Asset Contagion" reports.
The Problem: Many bearer tokens (like wrapped BTC or certain LSTs) rely on the solvency of the issuer or the bridge provider. If the bridge fails, the token becomes a "claim on nothing."
The rTRIO Advantage: Because of the 1:1 USDC Deterministic Ratio - the token isn't a "promise to pay"—it is a cryptographic proof of ownership of a specific portion of an anchored vault.
Overcoming the Inherent Insecurities of Cross-Chain Asset Movement:
Feature | Moving Assets (Legacy/Bridges) | Stationary Bearer Tokens (rTRIO) |
Security | High (Vulnerable "Honey Pot" contracts) | Maximum |
Legal | Ambiguous (Jurisdiction "moves" with token) | Certain |
Settlement | Slow (Requires cross-chain finality) | Instant (Only the "Right to Claim" changes hands) |
Risk | Bridge Exploits / De-pegging | Fiduciary Lock (Mathematically guaranteed) |



Comments